Table of Contents
You are about to use the equivalent of a microscope to look at the information that runs through the veins of a Windows network. We do more to observe the information than to interrogate it. When you are done with this primer, you should have a good understanding of the types of information that flow over the network. Do not worry, this is not a biology lesson. We won't lose you in unnecessary detail. Think to yourself, “This is easy,” then tackle each exercise without fear.
Samba can be configured with a minimum of complexity. Simplicity should be mastered before you get too deeply into complexities. Let's get moving: we have work to do.
Successful completion of this primer requires two Microsoft Windows 9x/Me Workstations as well as two Microsoft Windows XP Professional Workstations, each equipped with an Ethernet card connected using a hub. Also required is one additional server (either Windows NT4 Server, Windows 2000 Server, or a Samba-3 on UNIX/Linux server) running a network sniffer and analysis application (ethereal is a good choice). All work should be undertaken on a quiet network where there is no other traffic. It is best to use a dedicated hub with only the machines under test connected at the time of the exercises.
Ethereal has become the network protocol analyzer of choice for many network administrators. You may find more information regarding this tool from the Ethereal Web site. Ethereal installation files for Windows may be obtained from the Ethereal Web site. Ethereal is provided with SUSE and Red Hat Linux distributions, as well as with many other Linux distributions. It may not be installed on your system by default. If it is not installed, you may also need to install the libpcap software before you can install or use Ethereal. Please refer to the instructions for your operating system or to the Ethereal Web site for information regarding the installation and operation of Ethereal.
To obtain ethereal for your system, please visit the Ethereal download site.
Note
The successful completion of this chapter requires that you capture network traffic using Ethereal. It is recommended that you use a hub, not an Ethernet switch. It is necessary for the device used to act as a repeater, not as a filter. Ethernet switches may filter out traffic that is not directed at the machine that is used to monitor traffic; this would not allow you to complete the projects.
Do not worry too much if you do not have access to all this equipment; network captures from the exercises are provided on the enclosed CD-ROM. This makes it possible to dive directly into the analytical part of the exercises if you so desire.
Please do not be alarmed at the use of a high-powered analysis tool (Ethereal) in this primer. We expose you only to a minimum of detail necessary to complete the exercises. If you choose to use any other network sniffer and protocol analysis tool, be advised that it may not allow you to examine the contents of recently added security protocols used by Windows 200x/XP.
You could just skim through the exercises and try to absorb the key points made. The exercises provide all the information necessary to convince the die-hard network engineer. You possibly do not require so much convincing and may just want to move on, in which case you should at least read ???.
??? also provides useful information that may help you to avoid significantly time-consuming networking problems.
The purpose of this chapter is to create familiarity with key aspects of Microsoft Windows network computing. If you want a solid technical grounding, do not gloss over these exercises. The points covered are recurrent issues on the Samba mailing lists.
You can see from these exercises that Windows networking involves quite a lot of network broadcast traffic. You can look into the contents of some packets, but only to see some particular information that the Windows client sends to a server in the course of establishing a network connection.
To many people, browsing is everything that happens when one uses Microsoft Internet Explorer. It is only when you start looking at network traffic and noting the protocols and types of information that are used that you can begin to appreciate the complexities of Windows networking and, more importantly, what needs to be configured so that it can work. Detailed information regarding browsing is provided in the recommended preparatory reading.
Recommended preparatory reading: The Official Samba-3 HOWTO and Reference Guide, Second Edition (TOSHARG2) Chapter 9, “Network Browsing,” and Chapter 3, “Server Types and Security Modes.”
You are about to witness how Microsoft Windows computer networking functions. The exercises step through identification of how a client machine establishes a connection to a remote Windows server. You observe how Windows machines find each other (i.e., how browsing works) and how the two key types of user identification (share mode security and user mode security) are affected.
The networking protocols used by MS Windows networking when working with Samba use TCP/IP as the transport protocol. The protocols that are specific to Windows networking are encapsulated in TCP/IP. The network analyzer we use (Ethereal) is able to show you the contents of the TCP/IP packets (or messages).
Procedure 16.1. Diagnostic Tasks
Examine network traces to witness SMB broadcasts, host announcements, and name resolution processes.
Examine network traces to witness how share mode security functions.
Examine network traces to witness the use of user mode security.
Review traces of network logons for a Windows 9x/Me client as well as a domain logon for a Windows XP Professional client.
You are embarking on a course of discovery. The first part of the exercise requires
two MS Windows 9x/Me systems. We called one machine WINEPRESSME and the
other MILGATE98. Each needs an IP address; we used 10.1.1.10
and 10.1.1.11. The test machines need to be networked via a hub. A UNIX/Linux
machine is required to run Ethereal to enable the network activity to be captured.
It is important that the machine from which network activity is captured must not interfere with
the operation of the Windows workstations. It is helpful for this machine to be passive (does not
send broadcast information) to the network.
For these exercises, our test environment consisted of a SUSE 9.2 Professional Linux Workstation running VMWare 4.5. The following VMWare images were prepared:
Windows 98 name: MILGATE98
Windows Me name: WINEPRESSME
Windows XP Professional name: LightrayXP
Samba-3.0.20 running on a SUSE Enterprise Linux 9
Choose a workgroup name (MIDEARTH) for each exercise.
The network captures provided on the CD-ROM included with this book were captured using Ethereal
version 0.10.6. A later version suffices without problems, but an earlier version may not
expose all the information needed. Each capture file has been decoded and listed as a trace file. A summary of all
packets has also been included. This makes it possible for you to do all the studying you like without the need to
perform the time-consuming equipment configuration and test work. This is a good time to point out that the value
that can be derived from this book really does warrant your taking sufficient time to practice each exercise with
care and attention to detail.
In this section, we start a single Windows 9x/Me machine, then monitor network activity for 30 minutes.
Procedure 16.2. Monitoring Windows 9x Steps
Start the machine from which network activity will be monitored (using ethereal). Launch ethereal, click ->.
Click the following:
Update list of packets in real time
Automatic scrolling in live capture
Enable MAC name resolution
Enable network name resolution
Enable transport name resolution
Click .
Start the Windows 9x/Me machine to be monitored. Let it run for a full 30 minutes. While monitoring, do not press any keyboard keys, do not click any on-screen icons or menus, and do not answer any dialog boxes.
At the conclusion of 30 minutes, stop the capture. Save the capture to a file so you can go back to it later. Leave this machine running in preparation for the task in ???.
Analyze the capture. Identify each discrete message type that was captured. Note what transport protocol was used. Identify the timing between messages of identical types.
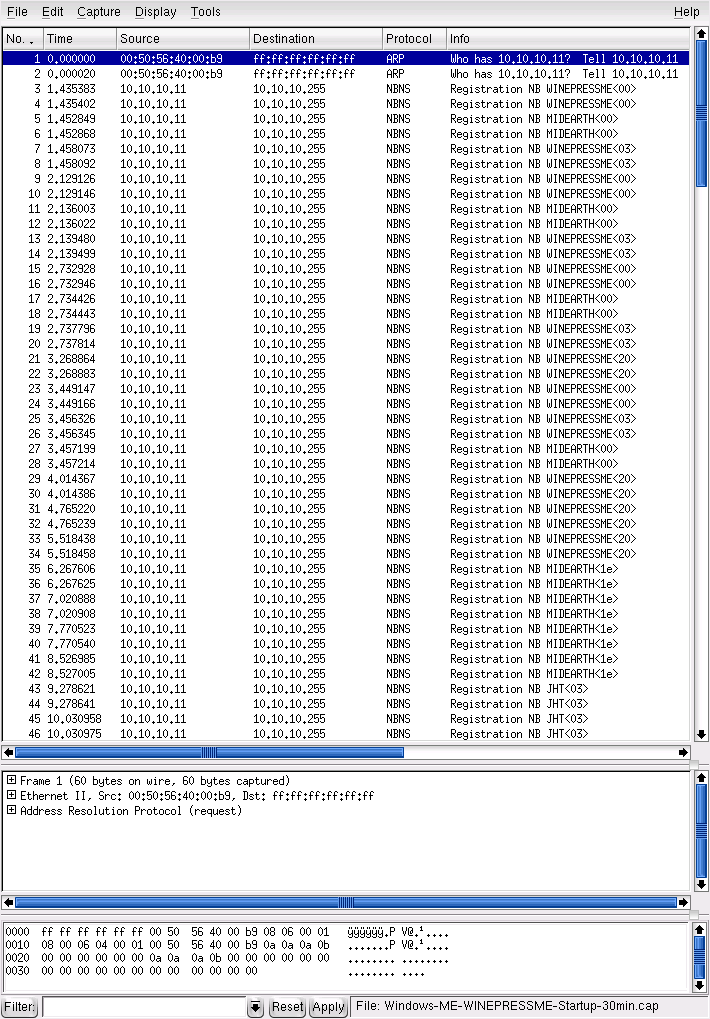
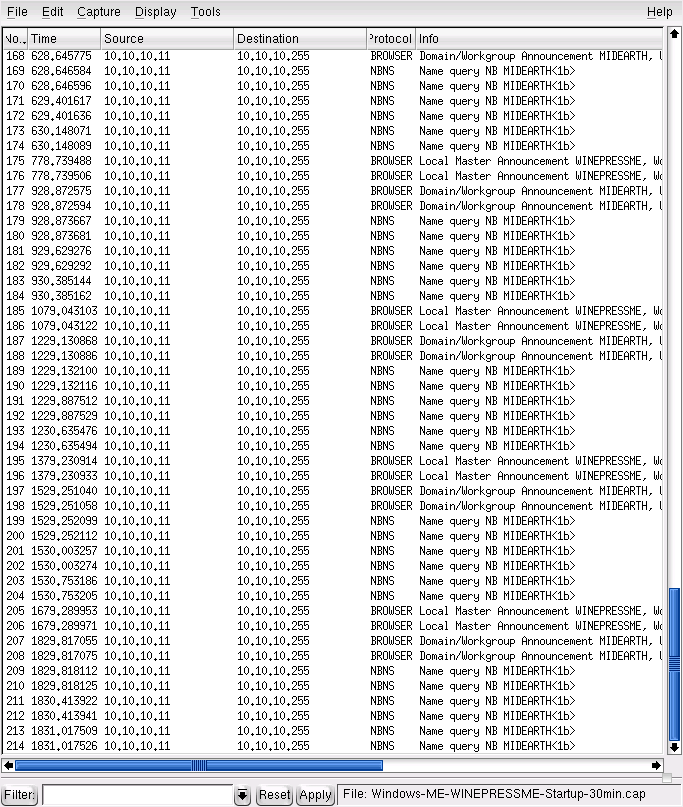
The summary of the first 10 minutes of the packet capture should look like ???. A screenshot of a later stage of the same capture is shown in ???.
Broadcast messages observed are shown in ???. Actual observations vary a little, but not by much. Early in the startup process, the Windows Me machine broadcasts its name for two reasons: first to ensure that its name would not result in a name clash, and second to establish its presence with the Local Master Browser (LMB).
Table 16.1. Windows Me Startup Broadcast Capture Statistics
| Message | Type | Num | Notes |
|---|---|---|---|
| WINEPRESSME<00> | Reg | 8 | 4 lots of 2, 0.6 sec apart |
| WINEPRESSME<03> | Reg | 8 | 4 lots of 2, 0.6 sec apart |
| WINEPRESSME<20> | Reg | 8 | 4 lots of 2, 0.75 sec apart |
| MIDEARTH<00> | Reg | 8 | 4 lots of 2, 0.75 sec apart |
| MIDEARTH<1d> | Reg | 8 | 4 lots of 2, 0.75 sec apart |
| MIDEARTH<1e> | Reg | 8 | 4 lots of 2, 0.75 sec apart |
| MIDEARTH<1b> | Qry | 84 | 300 sec apart at stable operation |
| __MSBROWSE__ | Reg | 8 | Registered after winning election to Browse Master |
| JHT<03> | Reg | 8 | 4 x 2. This is the name of the user that logged onto Windows |
| Host Announcement WINEPRESSME | Ann | 2 | Observed at 10 sec |
| Domain/Workgroup Announcement MIDEARTH | Ann | 18 | 300 sec apart at stable operation |
| Local Master Announcement WINEPRESSME | Ann | 18 | 300 sec apart at stable operation |
| Get Backup List Request | Qry | 12 | 6 x 2 early in startup, 0.5 sec apart |
| Browser Election Request | Ann | 10 | 5 x 2 early in startup |
| Request Announcement WINEPRESSME | Ann | 4 | Early in startup |
From the packet trace, it should be noted that no messages were propagated over TCP/IP; all messages employed UDP/IP. When steady-state operation has been achieved, there is a cycle of various announcements, re-election of a browse master, and name queries. These create the symphony of announcements by which network browsing is made possible.
For detailed information regarding the precise behavior of the CIFS/SMB protocols, refer to the book “Implementing CIFS: The Common Internet File System,” by Christopher Hertel, (Prentice Hall PTR, ISBN: 013047116X).
At this time, the machine you used to capture the single-system startup trace should still be running. The objective of this task is to identify the interaction of two machines in respect to broadcast activity.
Procedure 16.3. Monitoring of Second Machine Activity
On the machine from which network activity will be monitored (using ethereal), launch ethereal and click ->.
Click:
Update list of packets in real time
Automatic scrolling in live capture
Enable MAC name resolution
Enable network name resolution
Enable transport name resolution
Click .
Start the second Windows 9x/Me machine. Let it run for 15 to 20 minutes. While monitoring, do not press any keyboard keys, do not click any on-screen icons or menus, and do not answer any dialog boxes.
At the conclusion of the capture time, stop the capture. Be sure to save the captured data so you can examine the network data capture again at a later date should that be necessary.
Analyze the capture trace, taking note of the transport protocols used, the types of messages observed, and what interaction took place between the two machines. Leave both machines running for the next task.
??? summarizes capture statistics observed. As in the previous case, all announcements used UDP/IP broadcasts. Also, as was observed with the last example, the second Windows 9x/Me machine broadcasts its name on startup to ensure that there exists no name clash (i.e., the name is already registered by another machine) on the network segment. Those wishing to explore the inner details of the precise mechanism of how this functions should refer to “Implementing CIFS: The Common Internet File System.”
Table 16.2. Second Machine (Windows 98) Capture Statistics
| Message | Type | Num | Notes |
|---|---|---|---|
| MILGATE98<00> | Reg | 8 | 4 lots of 2, 0.6 sec apart |
| MILGATE98<03> | Reg | 8 | 4 lots of 2, 0.6 sec apart |
| MILGATE98<20> | Reg | 8 | 4 lots of 2, 0.75 sec apart |
| MIDEARTH<00> | Reg | 8 | 4 lots of 2, 0.75 sec apart |
| MIDEARTH<1d> | Reg | 8 | 4 lots of 2, 0.75 sec apart |
| MIDEARTH<1e> | Reg | 8 | 4 lots of 2, 0.75 sec apart |
| MIDEARTH<1b> | Qry | 18 | 900 sec apart at stable operation |
| JHT<03> | Reg | 2 | This is the name of the user that logged onto Windows |
| Host Announcement MILGATE98 | Ann | 14 | Every 120 sec |
| Domain/Workgroup Announcement MIDEARTH | Ann | 6 | 900 sec apart at stable operation |
| Local Master Announcement WINEPRESSME | Ann | 6 | Insufficient detail to determine frequency |
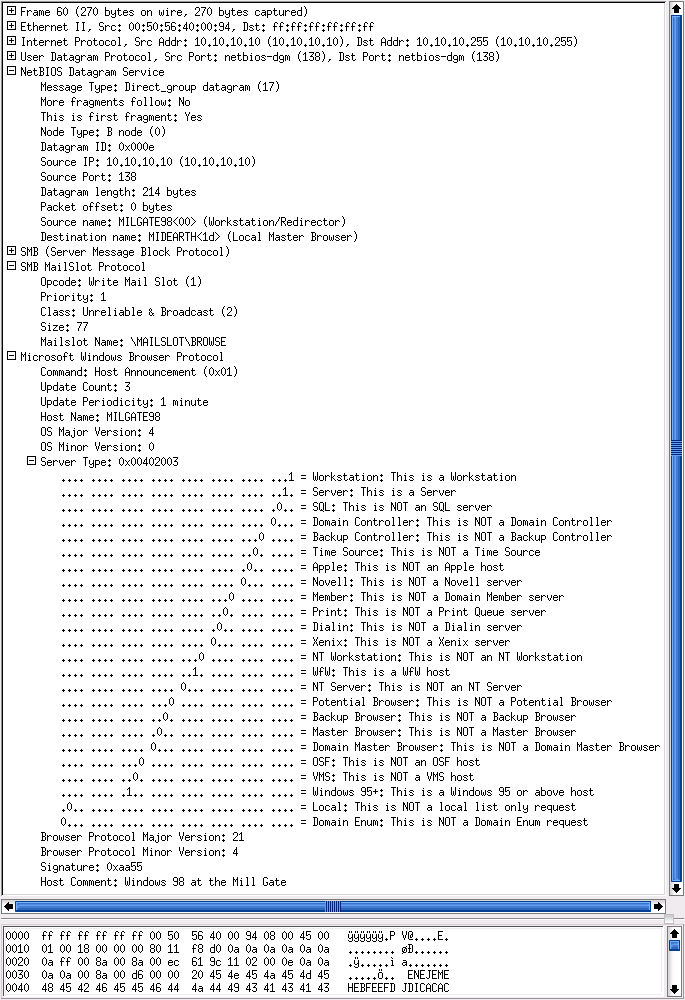
Observation of the contents of Host Announcements, Domain/Workgroup Announcements, and Local Master Announcements is instructive. These messages convey a significant level of detail regarding the nature of each machine that is on the network. An example dissection of a Host Announcement is given in ???.
The purpose of this exercise is to discover how Microsoft Windows clients create (establish) connections with remote servers. The methodology involves analysis of a key aspect of how Windows clients access remote servers: the session setup protocol.
Procedure 16.4. Client Connection Exploration Steps
Configure a Windows 9x/Me machine (MILGATE98) with a share called
Stuff. Create aFull Accesscontrol password on this share.Configure another Windows 9x/Me machine (WINEPRESSME) as a client. Make sure that it exports no shared resources.
Start both Windows 9x/Me machines and allow them to stabilize for 10 minutes. Log on to both machines using a user name (JHT) of your choice. Wait approximately 2 minutes before proceeding.
Start ethereal (or the network sniffer of your choice).
From the WINEPRESSME machine, right-click , select , select ->->->->. Enter the password you set for the
Full Controlmode for theStuffshare.When the share called
Stuffis being displayed, stop the capture. Save the captured data in case it is needed for later analysis.From the top of the packets captured, scan down to locate the first packet that has interpreted as
Session Setup AndX, User: anonymous; Tree Connect AndX, Path: \\MILGATE98\IPC$.In the dissection (analysis) panel, expand the
SMB, Session Setup AndX Request, and Tree Connect AndX Request. Examine both operations. Identify the name of the user Account and what password was used. The Account name should be empty. This is aNULLsession setup packet.Return to the packet capture sequence. There will be a number of packets that have been decoded of the type
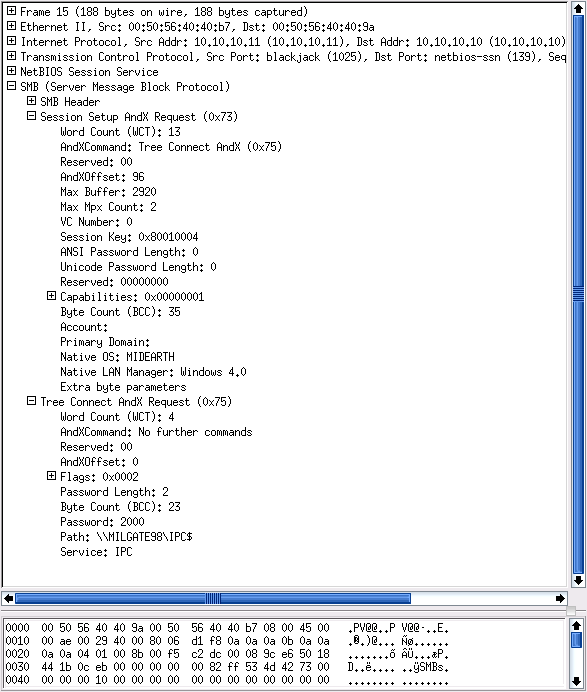
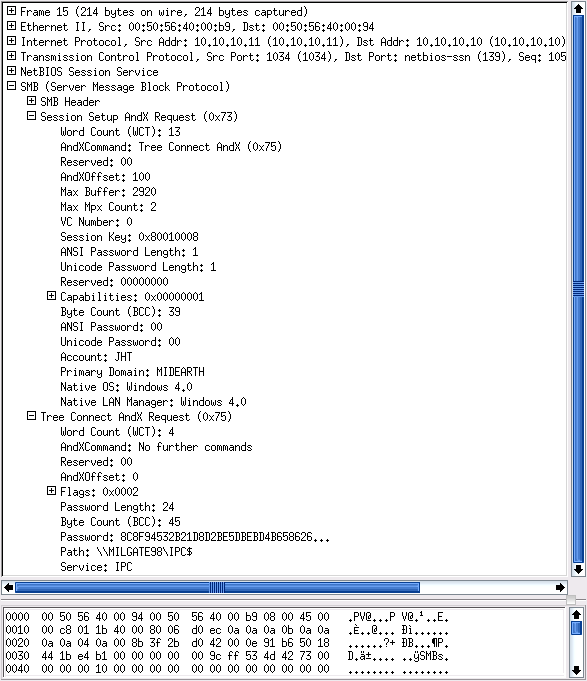
Session Setup AndX. Locate the last such packet that was targeted at the\\MILGATE98\IPC$service.Dissect this packet as per the previous one. This packet should have a password length of 24 (characters) and should have a password field, the contents of which is a long hexadecimal number. Observe the name in the Account field. This is a User Mode session setup packet.
The IPC$ share serves a vital purpose[15]
in SMB/CIFS-based networking. A Windows client connects to this resource to obtain the list of
resources that are available on the server. The server responds with the shares and print queues that
are available. In most but not all cases, the connection is made with a NULL
username and a NULL password.
The two packets examined are material evidence of how Windows clients may
interoperate with Samba. Samba requires every connection setup to be authenticated using
valid UNIX account credentials (UID/GID). This means that even a NULL
session setup can be established only by automatically mapping it to a valid UNIX
account.
Samba has a special name for the NULL, or empty, user account:
it calls it the guest account. The
default value of this parameter is nobody; however, this can be
changed to map the function of the guest account to any other UNIX identity. Some
UNIX administrators prefer to map this account to the system default anonymous
FTP account. A sample NULL Session Setup AndX packet dissection is shown in
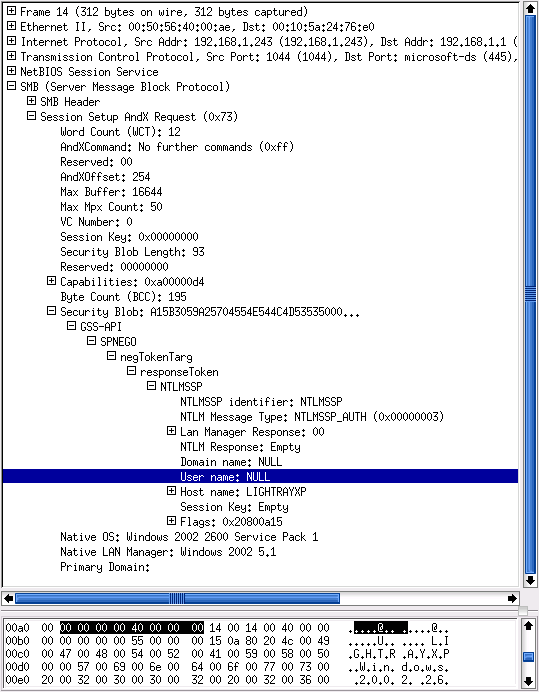
???.
When a UNIX/Linux system does not have a nobody user account
(/etc/passwd), the operation of the NULL
account cannot validate and thus connections that utilize the guest account
fail. This breaks all ability to browse the Samba server and is a common
problem reported on the Samba mailing list. A sample User Mode session setup AndX
is shown in ???.
The User Mode connection packet contains the account name and the domain name. The password is provided in Microsoft encrypted form, and its length is shown as 24 characters. This is the length of Microsoft encrypted passwords.
By now you may be asking, “Why did you choose to work with Windows 9x/Me?”
First, we want to demonstrate the simple case. This book is not intended to be a detailed treatise on the Windows networking protocols, but rather to provide prescriptive guidance for deployment of Samba. Second, by starting out with the simple protocol, it can be demonstrated that the more complex case mostly follows the same principles.
The following exercise demonstrates the case that even MS Windows XP Professional with up-to-date service
updates also uses the NULL account, as well as user accounts. Simply follow the procedure
to complete this exercise.
To complete this exercise, you need a Windows XP Professional client that has been configured as a domain member of either a Samba-controlled domain or a Windows NT4 or 200x Active Directory domain. Here we do not provide details for how to configure this, as full coverage is provided earlier in this book.
Procedure 16.5. Steps to Explore Windows XP Pro Connection Set-up
Start your domain controller. Also, start the ethereal monitoring machine, launch ethereal, and then wait for the next step to complete.
Start the Windows XP Client and wait 5 minutes before proceeding.
On the machine from which network activity will be monitored (using ethereal), launch ethereal and click ->.
Click:
Update list of packets in real time
Automatic scrolling in live capture
Enable MAC name resolution
Enable network name resolution
Enable transport name resolution
Click .
On the Windows XP Professional client, press to bring up the domain logon screen. Log in using valid credentials for a domain user account.
Now proceed to connect to the domain controller as follows: ->->->->->->->. Close the explorer window.
In this step, our domain name is
Midearth, the domain controller is calledFrodo, and we have connected to a share calleddata.Stop the capture on the ethereal monitoring machine. Be sure to save the captured data to a file so that you can refer to it again later.
If desired, the Windows XP Professional client and the domain controller are no longer needed for exercises in this chapter.
From the top of the packets captured, scan down to locate the first packet that has interpreted as
Session Setup AndX Request, NTLMSSP_AUTH.In the dissection (analysis) panel, expand the
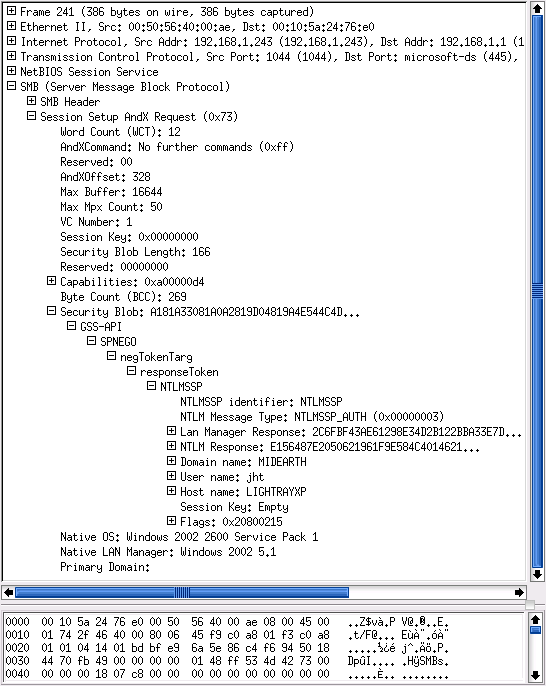
SMB, Session Setup AndX Request. Expand the packet decode information, beginning at theSecurity Blob:entry. Expand theGSS-API -> SPNEGO -> netTokenTarg -> responseToken -> NTLMSSPkeys. This should reveal that this is aNULLsession setup packet. TheUser name: NULLso indicates. An example decode is shown in ???.Return to the packet capture sequence. There will be a number of packets that have been decoded of the type
Session Setup AndX Request. Click the last such packet that has been decoded asSession Setup AndX Request, NTLMSSP_AUTH.In the dissection (analysis) panel, expand the
SMB, Session Setup AndX Request. Expand the packet decode information, beginning at theSecurity Blob:entry. Expand theGSS-API -> SPNEGO -> netTokenTarg -> responseToken -> NTLMSSPkeys. This should reveal that this is aUser Modesession setup packet. TheUser name: jhtso indicates. An example decode is shown in ???. In this case the user name wasjht. This packet decode includes theLan Manager Response:and theNTLM Response:. The values of these two parameters are the Microsoft encrypted password hashes: respectively, the LanMan password and then the NT (case-preserving) password hash.The passwords are 24-character hexadecimal numbers. This packet confirms that this is a User Mode session setup packet.
This exercise demonstrates that, while the specific protocol for the Session Setup AndX is handled
in a more sophisticated manner by recent MS Windows clients, the underlying rules or principles
remain the same. Thus it is demonstrated that MS Windows XP Professional clients still use a
NULL-Session connection to query and locate resources on an advanced network
technology server (one using Windows NT4/200x or Samba). It also demonstrates that an authenticated
connection must be made before resources can be used.
In summary, the following points have been established in this chapter:
When NetBIOS over TCP/IP protocols are enabled, MS Windows networking employs broadcast-oriented messaging protocols to provide knowledge of network services.
Network browsing protocols query information stored on browse masters that manage information provided by NetBIOS Name Registrations and by way of ongoing host announcements and workgroup announcements.
All Samba servers must be configured with a mechanism for mapping the
NULL-Sessionto a valid but nonprivileged UNIX system account.The use of Microsoft encrypted passwords is built right into the fabric of Windows networking operations. Such passwords cannot be provided from the UNIX
/etc/passwddatabase and thus must be stored elsewhere on the UNIX system in a manner that Samba can use. Samba-2.x permitted such encrypted passwords to be stored in thesmbpasswdfile or in an LDAP database. Samba-3 permits use of multiplepassdb backenddatabases in concurrent deployment. Refer to TOSHARG2, Chapter 10, “Account Information Databases.”
The exercises demonstrate the use of the guest account, the way that
MS Windows clients and servers resolve computer names to a TCP/IP address, and how connections
between a client and a server are established.
Those wishing background information regarding NetBIOS name types should refer to the Microsoft knowledgebase article Q102878.
The questions and answers given in this section are designed to highlight important aspects of Microsoft Windows networking.
- What is the significance of the MIDEARTH<1b> type query?
- What is the significance of the MIDEARTH<1d> type name registration?
- What is the role and significance of the <01><02>__MSBROWSE__<02><01> name registration?
- What is the significance of the MIDEARTH<1e> type name registration?
- guest account What is the significance of the guest account in smb.conf?
- Is it possible to reduce network broadcast activity with Samba-3?
- Can I just use plain-text passwords with Samba?
- What parameter in the smb.conf file is used to enable the use of encrypted passwords?
- Is it necessary to specify encrypt passwordsencrypt passwords = Yes when Samba-3 is configured as a domain member?
- Is it necessary to specify a guest account when Samba-3 is configured as a domain member server?